Maritime Cybersecurity Trained Professional (MarCybTPro) distance learning program
Overview
Modern ships and port facilities increasingly rely on digital technologies for navigation, communication, cargo handling, and operational management. On the positive side, this technological integration leads to amazing opportunities. On the negative side, it makes them more vulnerable to cyber threats.
Cyber-attacks can compromise critical systems on ships, such as navigation and engine controls. This leads to accidents, environmental disasters, and loss of life. Tampering with a ship's navigational system could lead to collisions or groundings.
Threat actors target the maritime sector for a variety of reasons. They engage in malicious activities aimed at exploiting, damaging, disrupting, or gaining unauthorized access to maritime operations, systems, and data. The methods and strategies used can be sophisticated and multifaceted.
The maritime sector is increasingly targeted by cybercriminals. Threats include malware, ransomware, data breaches, and interference with navigational systems. These can lead to significant financial losses, operational disruptions, and safety hazards. Organised crime groups increasingly use maritime routes for smuggling drugs, weapons, and humans.
Foreign intelligence agencies increasingly target the maritime sector for a variety of reasons, including geopolitical leverage, intelligence, and economic advantage. They use advanced cyber tools to infiltrate Information Technology (IT) and Operational Technology (OT) systems of ships, ports, and maritime companies. They target navigation systems, cargo management systems, and port operation networks. Once inside the network, they can steal sensitive data such as cargo details, trade secrets, blueprints of maritime technology, and security protocols. They also target suppliers or contractors in the maritime sector to gain access to their networks.
Nation-State Actors are foreign government-sponsored groups working for profit, geopolitical gains, intelligence, economic espionage, or disruption of the trade of rival nations. They possess sophisticated capabilities and can execute complex, well-funded cyber operations.
Human errors and the lack of cyber security awareness are two main factors leading to major cyber security incidents. Awareness and training can significantly reduce the likelihood and the impact of security breaches. Safe digital practices and threat recognition training are of paramount importance. Trained professionals respond effectively to cyber incidents, minimizing downtime, and facilitating quicker recovery.
Laws and regulations, including the NIS 2 Directive of the European Union, increasingly ask for more cyber resilience, awareness and training. Many standards and best practices have become regulatory obligations.
Target Audience
The program has been designed for:
- All maritime professionals who have authorised access to systems and data, working for Shipping Companies, Port Operators, Ocean Freight, Maritime Authorities.
- All maritime professionals who work for, or report to the Ship Security Officer (SSO), Company Security Officer (CSO), and Data Protection Officer (DPO).
- All IT managers and IT professionals working for the maritime industry.
- Vendors, suppliers and service providers, working with the maritime industry.
Course synopsis
Introduction.
- The MarCybTPro exam.
- The certificate of completion.
Part 1.
International Entities and Organizations shaping cybersecurity in the maritime industry.
- The International Maritime Organization (IMO).
- IMO, Guidelines on Maritime Cyber Risk Management.
- The Guidelines on Cyber Security Onboard Ships.
- The International Chamber of Shipping (ICS).
- The International Maritime Satellite Organization (Inmarsat).
Part 2.
US Entities shaping cybersecurity in the maritime industry.
- The US Congress.
- The U.S. Department of Homeland Security (DHS).
- DHS, U.S. Maritime Trade and Port Cybersecurity.
- The Cybersecurity and Infrastructure Security Agency (CISA).
- Marine Transportation System Resilience Assessment Guide (MTS Guide).
- The United States Coast Guard (USCG).
- USCG, Future B – Cybergeddon.
- 2022 Cyber Trends and Insights in the Marine environment, from the Coast Guard Cyber Command.
- Advantage at Sea, Prevailing with Integrated All-Domain Naval Power.
- Maritime Cybersecurity Assessment and Annex Guide (MCAAG).
- The Maritime Administration (MARAD).
- Maritime Transportation Security Act (MTSA) of 2002.
Part 3.
EU Entities shaping cybersecurity in the maritime industry.
- The decision-making institutions.
- Delegated acts, Implementing acts.
- The European Network and Information Security Agency (ENISA).
- Europol, EMPACT.
- TIBER-EU – The European framework for Threat Intelligence-based Ethical Red Teaming.
- The European Maritime Safety Agency (EMSA).
- EMSA, Interim Guidance on Maritime Security for Member States’ Competent Authorities, 2023.
- 10 March 2023, European Commission, Joint communication.
- The NIS 2 Directive of the EU.
- Entities in the scope of NIS 2.
- “Inland, sea and coastal passenger and freight water transport companies, not including the individual vessels operated by those companies”,
- “Managing bodies of ports, including their port facilities, and entities operating works and equipment contained within ports”,
- “Operators of vessel traffic services (VTS)”.
Part 4.
UK Entities shaping cybersecurity in the maritime industry.
- The UK Parliament, the Department for Transport (DfT).
- DfT, Cyber Security Code of Practice for Ships (COP).
- The Maritime and Coastguard Agency (MCA).
Part 5.
Modus Operandi.
- Step 1 – Collecting information about persons and systems.
- Ideologies and cyber risk.
- Employee collusion with external parties.
- Step 2 – Identifying possible targets and victims.
- Step 3 – Evaluation, recruitment and testing.
- Step 4 - Privilege escalation.
- Step 5 – Identifying important clients and stakeholders.
- Step 6 – Critical infrastructure.
- Case Studies.
- Social Engineering.
- Reverse Social Engineering.
- Phishing.
- Clone phishing.
- Spear-phishing.
- Whaling – Phishing for executives.
- Smishing and Vishing Attacks.
Part 6.
The NIST Cybersecurity Framework.
- Framework for Improving Critical Infrastructure Cybersecurity, Version 1.1.
- 1. The Framework Core.
- 2. The Framework Implementation Tiers.
- 3. The Framework Profiles.
- Coordination of Framework Implementation.
- How to Use the Framework.
- Communicating Cybersecurity Requirements with Stakeholders.
- Methodology to Protect Privacy and Civil Liberties.
- NIST Privacy Framework: A Tool for Improving Privacy through Enterprise Risk Management.
- Privacy Risk Management.
- Privacy Framework Basics.
- How to Use the Privacy Framework.
- Determining Privacy Capabilities.
- The NIST Cybersecurity Framework 2.0.
Part 7.
Case Studies - Cyber attacks against maritime targets.
- NotPetya.
- Port of Antwerp.
- Joint report of Europol and the Security Steering Committee of the ports of Antwerp, Hamburg / Bremerhaven and Rotterdam, 30 March 2023.
Understanding Cyber Espionage.
- Political, Economic, Military Intelligence.
- UK, Centre for the Protection of National Infrastructure (CPNI) – Espionage.
- Espionage and other intelligence activities, Bundesamt für Verfassungsschutz (BfV, the German Federal Office for the Protection of the Constitution).
Misinformation, disinformation, deception management, fabrication.
- Disinformation management.
- ENISA, Disinformation operations in cyber-space.
- ENISA, Active Defence and Offensive Countermeasures.
Closing remarks.
Become a Maritime Cybersecurity Trained Professional (MarCybTPro)
This is a Distance Learning with Certificate of Completion program, provided by Cyber Risk GmbH. The General Terms and Conditions for all legal transactions made through the Cyber Risk GmbH websites (hereinafter “GTC”) can be found at: https://www.cyber-risk-gmbh.com/Impressum.html
Each Distance Learning with Certificate of Completion program (hereinafter referred to as “distance learning program”) is provided at a fixed price, that includes VAT. There is no additional cost, now or in the future, for any reason.
We will send the distance learning program via email up to 24 hours after the payment (working days). Please remember to check the spam folder of your email client too, as emails with attachments are often landed in the spam folder.
You have the option to ask for a full refund up to 60 days after the payment. If you do not want one of our distance learning programs for any reason, all you must do is to send us an email, and we will refund the payment, no questions asked.
Your payment will be received by Cyber Risk GmbH (Dammstrasse 16, 8810 Horgen, Switzerland, Handelsregister des Kantons Zürich, Firmennummer: CHE-244.099.341). Cyber Risk GmbH will also send the certificates of completion to all persons that will pass the exam.
The all-inclusive cost is 297 USD (US Dollars). There is no additional cost, now or in the future, for this program.
First option: You can purchase the Maritime Cybersecurity Trained Professional (MarCybTPro) program with VISA, MASTERCARD, AMEX, Apple Pay, Google Pay etc.
Purchase the MarCybTPro program here (VISA, MASTERCARD, AMEX, Apple Pay, Google Pay etc.)Second option: QR code payment.
i. Open the camera app or the QR app on your phone.
ii. Scan the QR code and possibly wait for a few seconds.
iii. Click on the link that appears, open your browser, and make the payment.

What is included in the cost of the distance learning program:
A. The official presentations (1207 slides).
The presentations are effective and appropriate to study online or offline. Busy professionals have full control over their own learning and are able to study at their own speed. They are able to move faster through areas of the course they feel comfortable with, but slower through those that they need a little more time on.
B. Up to 3 online exam attempts per year.
Candidates must pass only one exam. If they fail, they must study the official presentations and retake the exam. Candidates are entitled to 3 exam attempts every year.
If candidates do not achieve a passing score on the exam the first time, they can retake the exam a second time.
If they do not achieve a passing score the second time, they can retake the exam a third time.
If candidates do not achieve a passing score the third time, they must wait at least one year before retaking the exam. There is no additional cost for additional exam attempts.
To learn more, you may visit:
https://www.maritime-cybersecurity.com/Distance_Learning_Programs_Exam_Certificate_of_Completion.pdf
C. The certificate of completion, with a scannable QR code for verification.
You will receive your certificate via email in Adobe Acrobat format (pdf), with a scannable QR code for verification, 7 business days after you pass the exam. A business day refers to any day in which normal business operations are conducted (in our case Monday through Friday), excluding weekends and public holidays.
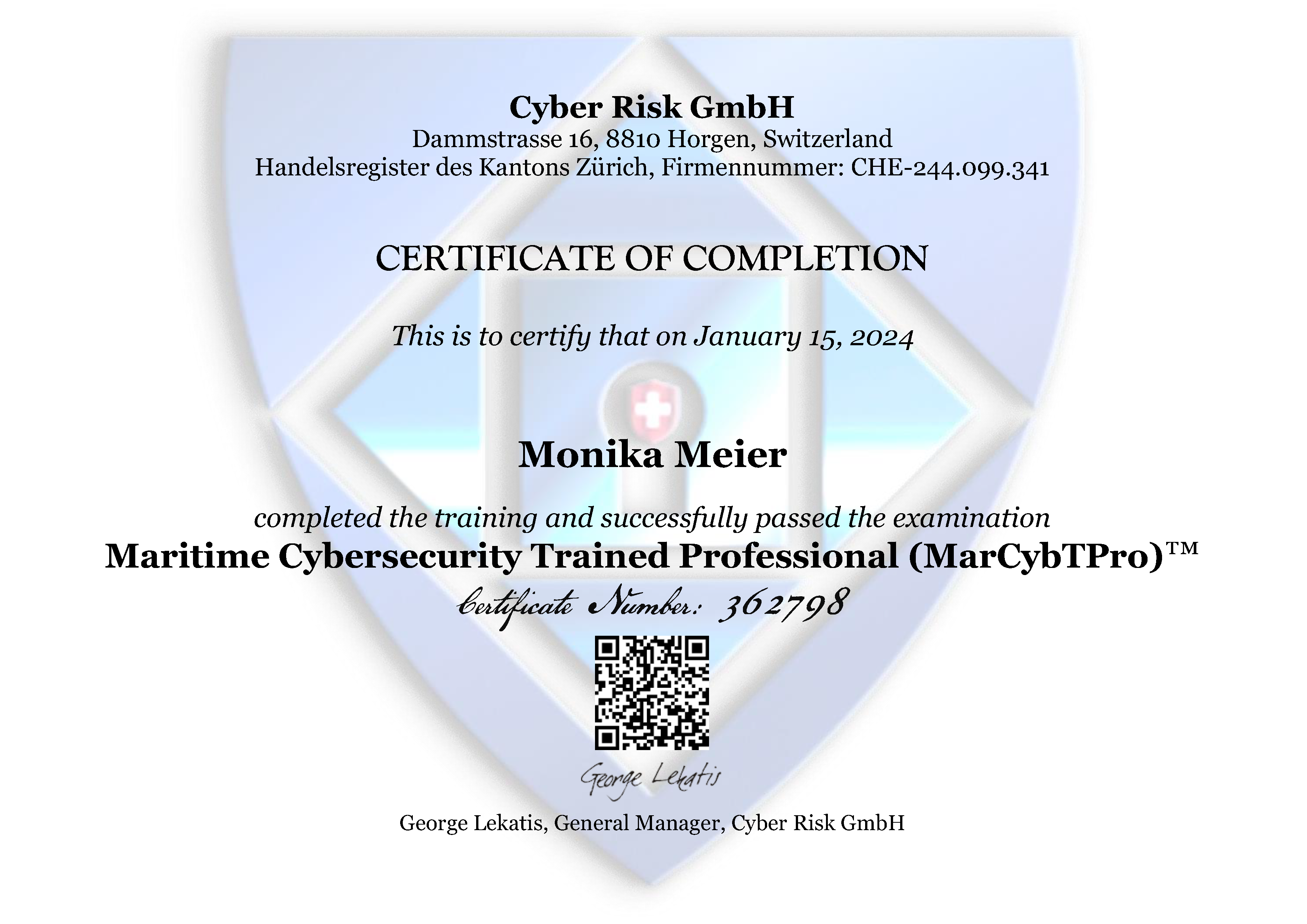
D. Cyber Risk GmbH will develop a web page dedicated to each certified professional (https://www.cyber-risk-gmbh.com/Your_Name.htm).
When third parties scan the QR code on your certificate, they will visit this web page (https://www.cyber-risk-gmbh.com/Your_Name.htm), and they will be able to verify that you are a certified professional, and your certificates are valid and legitimate.
In this web page we will have your name, all the certificates you have received from us, and pictures of your certificates.
This is an example:
https://www.cyber-risk-gmbh.com/Monika_M_Meier.html
You can print your certificate that you will receive in Adobe Acrobat format (pdf). With the scannable QR code, all third parties can verify the authenticity of each certificate in a matter of seconds. Professional certificates are some of the most frequently falsified documents. Employers and third parties need an easy, effective, and efficient way to check the authenticity of each certificate. QR code verification is a good response to this demand.
Frequently Asked Questions for the distance learning programs.
1. I want to know more about Cyber Risk GmbH.
Cyber Risk GmbH is a company incorporated in Switzerland.
Company number: CHE-244.099.341.
Cantonal Register of Commerce: Canton of Zürich.
Registered address: Dammstrasse 16, 8810 Horgen, Switzerland.
Swiss VAT number: CHE-244.099.341 MWST.
EU VAT number: EU276036462. Cyber Risk GmbH is registered for EU VAT purposes in Germany (Bundeszentralamt für Steuern, Verfahren One-Stop-Shop, Nicht EU-Regelung) for the sale of services in the EU. Cyber Risk GmbH declares and pays EU VAT in a single electronic quarterly return submitted to Germany, and the German Bundeszentralamt für Steuern forwards the EU VAT due to each member State of the EU.
The owner and general manager of Cyber Risk GmbH is George Lekatis, a well-known expert in risk management and compliance. George is also the general manager of Compliance LLC, incorporated in Wilmington, NC, and offices in Washington, DC. It is a provider of risk and compliance training and executive coaching in 57 countries.
Several business units of Compliance LLC are very successful associations that offer membership, weekly or monthly updates, training, certification, Authorized Certified Trainer (ACT) programs, and other services to their members.
The business units of Compliance LLC include:
- The Sarbanes-Oxley Compliance Professionals Association (SOXCPA), the largest Association of Sarbanes-Oxley professionals in the world. You may visit: https://www.sarbanes-oxley-association.com
- The Basel iii Compliance Professionals Association (BiiiCPA), the largest association of Basel iii Professionals in the world. You may visit: https://www.basel-iii-association.com
- The Solvency II Association, the largest association of Solvency II professionals in the world. You may visit: https://www.solvency-ii-association.com
- The International Association of Risk and Compliance Professionals (IARCP). You may visit: https://www.risk-compliance-association.com
The Certified Risk and Compliance Management Professional (CRCMP) program, from the IARCP, has become one of the most recognized certificates in risk management and compliance. There are CRCMPs in 57 countries. Companies and organizations around the world consider the CRCMP a preferred certificate.
You can find more about the demand for CRCMPs at: https://www.risk-compliance-association.com/CRCMP_Jobs_Careers.pdf
“Cyber Risk GmbH Training Programs” are training programs developed, updated and provided by Cyber Risk GmbH, and include:
a) In-House Instructor-Led Training programs,
b) Online Live Training programs,
c) Video-Recorded Training programs,
d) Distance Learning with Certificate of Completion programs.
“Cyber Risk GmbH websites” are all websites that belong to Cyber Risk GmbH, and include the following:
a. Sectors and Industries.
2. Social Engineering Training
12. Transport Cybersecurity Toolkit
14. Sanctions Risk
15. Travel Security
b. Understanding Cybersecurity.
4. What is Synthetic Identity Fraud?
c. Understanding Cybersecurity in the European Union.
2. The Digital Operational Resilience Act (DORA)
3. The Critical Entities Resilience Directive (CER)
5. The European Data Governance Act (DGA)
6. The European Cyber Resilience Act (CRA)
7. The Digital Services Act (DSA)
8. The Digital Markets Act (DMA)
10. The Artificial Intelligence Act
11. The Artificial Intelligence Liability Directive
12. The Framework for Artificial Intelligence Cybersecurity Practices (FAICP)
13. The EU Cyber Solidarity Act
14. The Digital Networks Act (DNA)
15. The European ePrivacy Regulation
16. The European Digital Identity Regulation
17. The European Media Freedom Act (EMFA)
18. The Corporate Sustainability Due Diligence Directive (CSDDD)
19. The European Health Data Space (EHDS)
20. The European Financial Data Space (EFDS)
21. The Financial Data Access (FiDA) Regulation
22. The Payment Services Directive 3 (PSD3), Payment Services Regulation (PSR)
23. The European Cyber Defence Policy
24. The Strategic Compass of the European Union
25. The EU Cyber Diplomacy Toolbox
2. Is there any discount available for the distance learning programs?
We do not offer a discount for your first program, as we want to keep the cost as low as possible. You have a $100 discount for your second and each additional program.
After you purchase the Maritime Cybersecurity Trained Professional (MarCybTPro) program at $297, you can purchase your second and each additional distance learning program at $197.
3. Are there any entry requirements or prerequisites required for enrolling in the training programs?
There are no entry requirements or prerequisites for enrollment. Our programs give the opportunity to individuals of all levels to learn, grow, and develop new skills without the need for prior qualifications or specific experience.
4. I want to learn more about the exam.
You can take the exam online from your home or office, in all countries.
It is an open book exam. Risk and compliance management is something you must understand and learn, not memorize. You must acquire knowledge and skills, not commit something to memory.
You will be given 90 minutes to complete a 35-question exam. You must score 70% or higher.
The exam contains only questions that have been clearly answered in the official presentations.
All exam questions are multiple-choice, composed of two parts:
a. A stem (a question asked, or an incomplete statement to be completed).
b. Four possible responses.
In multiple-choice questions, you must not look for a correct answer, you must look for the best answer. Cross out all the answers you know are incorrect, then focus on the remaining ones. Which is the best answer? With this approach, you save time, and you greatly increase the likelihood of selecting the correct answer.
TIME LIMIT - This exam has a 90-minute time limit. You must complete this exam within this time limit, otherwise the result will be marked as an unsuccessful attempt.
BACK BUTTON - When taking this exam you are NOT permitted to move backwards to review/change prior answers. Your browser back button will refresh the current page instead of moving backward.
RESTART/RESUME – You CANNOT stop and then resume the exam. If you stop taking this exam by closing your browser, your answers will be lost, and the result will be marked as an unsuccessful attempt.
SKIP - You CANNOT skip answering questions while taking this exam. You must answer all the questions in the order the questions are presented.
When you are ready to take the exam, you must follow the steps described at "Question h. I am ready for the exam. What must I do?", at:
https://www.maritime-cybersecurity.com/Distance_Learning_Programs_Exam_Certificate_of_Completion.pdf
5. How comprehensive are the presentations? Are they just bullet points?
The presentations are not bullet points. They are effective and appropriate to study online or offline.
6. Do I need to buy books to pass the exam?
No. If you study the presentations, you can pass the exam. All the exam questions are clearly answered in the presentations. If you fail the first time, you must study more. Print the presentations and use Post-it to attach notes, to know where to find the answer to a question.
7. Is it an open book exam? Why?
Yes, it is an open book exam. Risk and compliance management is something you must understand and learn, not memorize. You must acquire knowledge and skills, not commit something to memory.
8. Do I have to take the exam soon after receiving the presentations?
No. You can take the exam any time. Your account never expires. You have lifetime access to the training program. If there are any updates to the training material and you have not passed the exam, you will receive the updated program free of charge.
9. Do I have to spend more money in the future keep my certificate of completion valid?
No. Your certificate of completion will remain valid, without the need to spend money or to take another exam in the future.
10. Ok, the certificate of completion never expires, but things change.
Recertification would be a great recurring revenue stream for Cyber Risk GmbH, but it would also be a recurring expense for our clients. We resisted the temptation to "introduce multiple recurring revenue streams to keep business flowing", as we were consulted. No recertification is needed for our programs.
Things change, and this is the reason you need to visit the "Reading Room" of Cyber Risk GmbH every month, and read the monthly newsletter with updates, alerts, and opportunities, to stay current. You may visit:
https://www.cyber-risk-gmbh.com/Reading_Room.html
11. Which is your refund policy?
Cyber Risk GmbH has a very clear refund policy: You have the option to ask for a full refund up to 60 days after the payment. If you do not want one of our programs for any reason, all you must do is to send us an email, and we will refund the payment after one business day, no questions asked.
12. I want to receive a printed certificate. Can you send me one?
Unfortunately this is not possible. You will receive your certificate via email in Adobe Acrobat format (pdf), with a scannable QR code for verification, 7 business days after you pass the exam. A business day refers to any day in which normal business operations are conducted (in our case Monday through Friday), excluding weekends and public holidays.
Cyber Risk GmbH will develop a dedicated web page for each professional (https://www.cyber-risk-gmbh.com/Your_Name.html). In your dedicated web page we will add your full name, all the certificates you have received from Cyber Risk GmbH, and the pictures of your certificates.
When third parties scan the QR code on your certificate, they will visit your dedicated web page, and they will be able to verify that you are a certified professional, and your certificates are valid and legitimate.
Professional certificates are some of the most frequently falsified documents. Employers and third parties need an easy, effective, and efficient way to check the authenticity of each certificate. QR code verification is a good response to this demand.
You can print your certificate that you will receive in Adobe Acrobat format. With the scannable QR code, all third parties can verify the authenticity of each certificate in a matter of seconds.
13. Why should I choose your training programs?
a. The maritime sector is increasingly targeted by cybercriminals. Our target audience is overwhelmed and has little time to spare. Cyber Risk GmbH has developed training programs that can assist professionals in understanding the regulatory expectations, risks and controls, but also in providing evidence that they are qualified, as they must pass an exam to receive the certificate of completion.
b. Our training programs are flexible and convenient. Learners can access the course material and take the exam at any time and from any location. This is especially important for those with busy schedules.
c. The all-inclusive cost of our programs is very low. There is no additional cost for each program, now or in the future, for any reason.
d. If you purchase a second program, you have a $100 discount. The all-inclusive cost for your second (and each additional) program is $197.
e. There are 3 exam attempts per year that are included in the cost of each program, so you do not have to spend money again if you fail.
f. No recertification is required. Your certificates of completion never expire.
g. The marketplace is clearly demanding qualified professionals in risk and compliance management. Certified professionals enjoy industry recognition and have more and better job opportunities.
h. Firms and organizations hire and promote fit and proper professionals who can provide evidence that they are qualified. Employers need assurance that managers and employees have the knowledge and skills needed to mitigate risks and accept responsibility. Supervisors and auditors ask for independent evidence that the process owners are qualified, and that the controls can operate as designed, because the persons responsible for these controls have the necessary knowledge and experience.
i. Professionals that gain more skills and qualifications often become eligible for higher-paying roles. Investing in training can have a direct positive impact on a manager's or employee's earning potential.